Genesis Block Hash: What It Is and Why It Matters in Blockchain
When you hear genesis block hash, the unique cryptographic fingerprint of the first block in a blockchain. It's not just a string of letters and numbers—it's the anchor of trust for the entire network. Without it, there’s no chain. No Bitcoin. No Ethereum. No verifiable history. This one hash proves the chain started exactly as designed, and nothing before it exists.
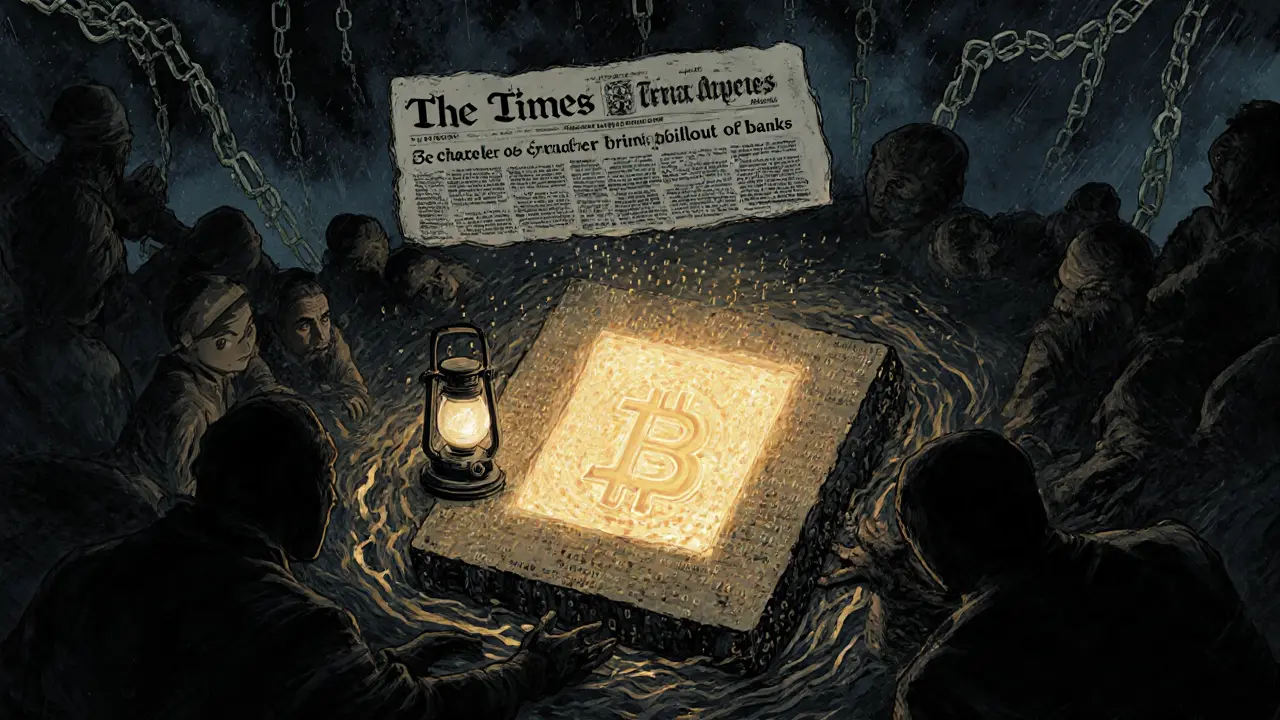
Every block after the genesis block links back to it through cryptographic hashes. That’s how blockchains stay tamper-proof. If someone tried to change a single transaction from 2009, the hash of the second block would break, then the third, then all the way forward. The Bitcoin genesis block, the first block ever mined by Satoshi Nakamoto on January 3, 2009, contains a hidden message in its coinbase transaction: "The Times 03/Jan/2009 Chancellor on brink of second bailout for banks." That’s not a coincidence. It’s a timestamp, a protest, and a proof that this chain was born outside the old system.
The cryptographic hash, a one-way function that turns any input into a fixed-length string used for the genesis block is created using SHA-256. It’s impossible to reverse-engineer the original data from it. That’s why even a tiny change in the block’s content—like adding a space—would produce a completely different hash. This is why the genesis block hash is sacred. No miner, no company, no government can alter it. It’s a digital artifact, frozen in time.
Today, every new blockchain—whether it’s built for gaming, finance, or identity—starts with its own genesis block hash. Some are public, like Bitcoin’s. Others are private, used by enterprises to build permissioned networks. But they all follow the same rule: the first block sets the tone. It’s the origin point for every transaction, every wallet, every smart contract that comes after.
That’s why you’ll see people checking genesis block hashes when they audit a new coin. Is this chain really new? Or is it a copy-paste job with fake history? A real genesis block hash can’t be faked. It’s tied to the exact moment the network went live. And if the hash doesn’t match what’s documented in the whitepaper or GitHub repo? That’s a red flag.
In the posts below, you’ll find real-world examples of how this concept shows up in crypto today—from chains built by Sony to tokens that claim to be new but have no verifiable origin. You’ll see how identity systems rely on blockchain roots, how exchanges verify chain integrity, and why scams often fail to fake the genesis. This isn’t theory. It’s the bedrock of what makes crypto trustworthy—or not.