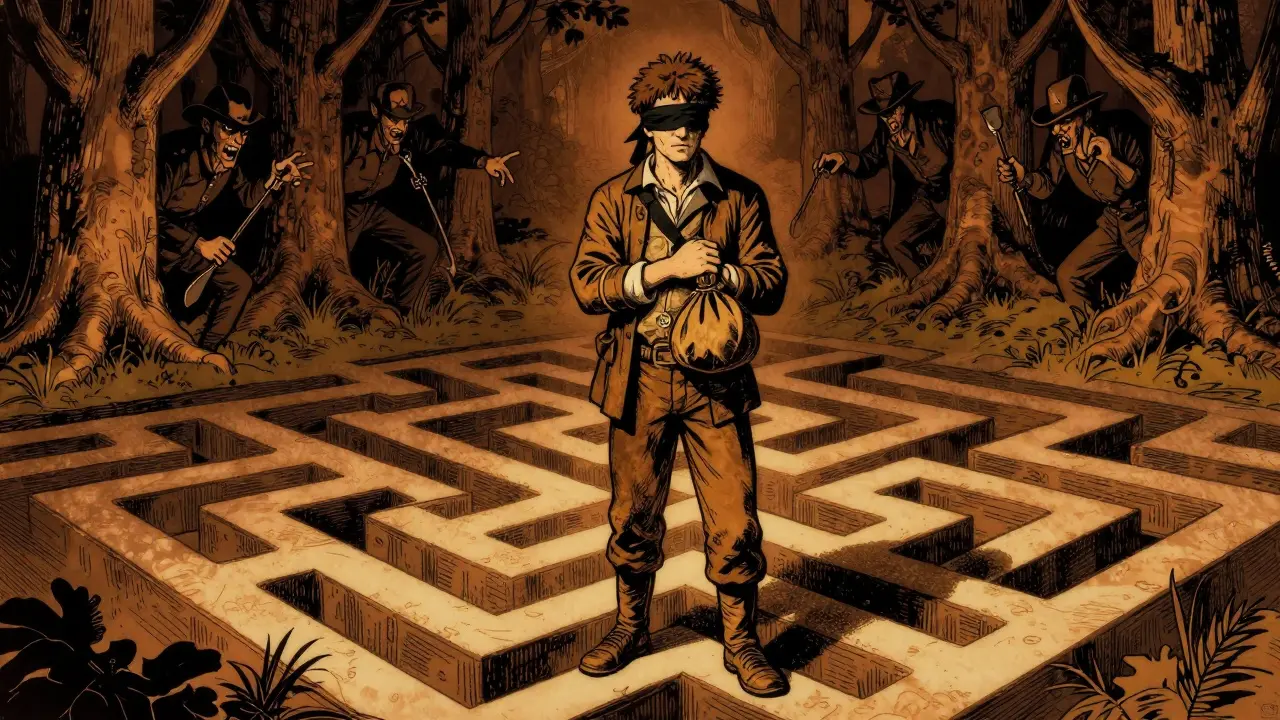
You might think moving money between blockchains is as easy as swapping dollars for euros at a currency kiosk. In reality, the process is closer to navigating a maze blindfolded while thieves try to pick your pockets. This is the harsh reality of Cross-Chain Technology, which connects isolated digital ledgers but struggles under massive security and technical pressure. As we move through 2026, the demand to move assets faster than ever has created a perfect storm of vulnerabilities. With over $19 billion locked in bridges alone last year, the stakes couldn't be higher. If you are looking to build, invest, or regulate in this space, understanding the friction is just as vital as knowing the benefits.
The Promise vs. The Reality of Interoperability
At its core, interoperability solves a single, glaring problem: fragmentation. Without tools to link networks, every blockchain exists in a silo. You hold Bitcoin here, but the best lending protocols live there. Early pioneers like Cosmos launched their Inter-Blockchain Communication protocol in 2021 to fix this, followed closely by Polkadot's relay chain approach. The theory was beautiful. In practice, the execution is fraught with hidden complexities.
The market has responded aggressively to this gap. By early 2025, the top five protocols were controlling nearly 70% of the total value locked across chains. However, growth has exposed structural weaknesses that developers knew were there all along. We aren't seeing smooth highways connecting these islands yet; we are building rickety rope bridges over active volcanoes. While legitimate commerce drives billions in volume, the infrastructure is struggling to keep up with both the speed of users and the sophistication of attackers.
Why Security Keeps Falling Short
If you ask any security researcher about the weak point in the crypto ecosystem, they will point straight at the bridge. Blockchain Bridges act as the entryways between ecosystems, making them high-value targets for hackers. We've seen time and again that these systems are prime hunting grounds. Just look at the history of Wormhole or the exploits involving the bZx protocol, where attackers moved millions through multiple chains to obscure their trail.
It isn't just about theft; it's about the fundamental architecture. There are two main ways to build these connections, and neither is perfect. Trusted bridges rely on centralized custodians to manage keys, which brings back the risk of a single point of failure. On the other hand, trustless models use complex cryptographic proofs. These avoid central points of failure but introduce extreme technical complexity that is prone to bugs. Dr. Wei Wang from Stanford noted after analyzing dozens of major bridge exploits that these mechanisms remain the most vulnerable component in the multi-chain environment. Simply put, adding more layers to code means adding more places for things to break.
Technical Friction and Scalability Issues
Beyond getting hacked, the technology often just feels slow or broken. Half of the interoperability protocols suffer from severe scalability issues when traffic spikes. Imagine trying to move funds during a bull run only to find transaction times delay by hours. Reports from late 2025 show significant degradation in user experience during peak periods, with delays costing users thousands in lost opportunities.
Data standards add another layer of confusion. There is no universal rulebook for how Chain A talks to Chain B. About 80% of projects still struggle to integrate because the lack of standardized protocols makes development resource-intensive. It forces developers to rewrite code for every single connection they want to support. This leads to a fragmented landscape where even basic tasks like tracking a stablecoin become a nightmare for legacy analytics tools.
| Feature | Trusted Bridges | Trustless Bridges |
|---|---|---|
| Security Model | Centralized Custody | Cryptographic Proof |
| Decentralization | Low | High |
| Complexity | Lower Setup | Extreme Implementation |
| Typical Risk | Insider Threat/Custody | Code Exploits/Bugs |

The Regulatory Black Hole
Perhaps the biggest hurdle isn't technical at all-it's legal. Governments require compliance with Anti-Money Laundering (AML) laws, but the technology currently creates "blind spots" that regulators hate. Illicit flows have surged, with over $21 billion laundered through cross-chain services recently. When funds jump from Ethereum to Binance Smart Chain via a bridge, traditional tracking tools lose the trail completely. Elliptic's research highlights that transparency drops significantly when destination addresses change formats across different networks.
This disconnect forces a choice between privacy and visibility. Companies like KYC-Chain argue that legacy systems cannot maintain a contiguous tracking record across chains. Law enforcement agencies are constantly chasing funds that vanish into alternate blockchains. For businesses, this uncertainty is paralyzing. Over 70% of enterprises cite unclear regulations as the main barrier to adoption. They don't know if sharing data across chains violates GDPR or CCPA, creating a compliance deadlock that stalls enterprise deployment.
What It Feels Like for the User
We need to stop talking about "nodes" and talk about frustration. Real people are losing money and patience. Recent surveys indicate that 35% of users face difficulties just navigating these interfaces. One documented case involved a user trying to move a modest sum from Ethereum to Polygon. It took nearly 47 minutes, three failed attempts, and cost significantly more in gas fees than the transfer was worth.
Customer support is equally elusive. When a bridge fails, users have nowhere to call. Reviews average less than 3 stars, with common complaints citing unexpected failures and silence during outages. Positive experiences exist-whales moving millions successfully-but the average small investor hits a wall of errors. Documentation varies wildly too, with some leading protocols scoring poorly on usability guides, leaving users guessing when a transaction hangs indefinitely.

The Path Forward
Solving these issues requires more than patching bugs. We need unified standards. Sidechain adoption is projected to grow significantly, but without a baseline agreement on interoperability, we risk splintering further. The European Union is pushing frameworks expected to set global standards for monitoring by late 2025, which could finally force the industry to clean up its act. Until then, users should treat cross-chain moves as high-risk operations. Diversify your chains, check the audit status of the bridge carefully, and always test with a small amount before committing real capital.
Frequently Asked Questions
What is the biggest risk of using cross-chain bridges?
The primary risk is security exploits targeting the bridge contracts themselves. Historical data shows bridges are the most vulnerable entry points for hackers compared to individual blockchain networks, often resulting in total loss of transferred funds.
Why do cross-chain transactions take so long?
Delays happen because the system waits for finality confirmations on the source chain before locking funds, then verifies those locks on the destination chain. During high-traffic periods, this confirmation process slows down significantly due to congestion.
Are cross-chain transfers private?
Most public cross-chain transactions are visible on the blockchain, making them traceable by third-party analytics firms. However, the complexity of jumping between chains sometimes obscures the full path of funds from standard regulators.
How do companies deal with regulatory compliance across chains?
Companies are adopting specialized behavioral risk detection tools that track entity movement across different networks. However, standardization remains a challenge, forcing many to operate with heightened scrutiny or manual reporting processes.
Which bridge type is safer, trusted or trustless?
Neither is inherently safer. Trusted bridges carry custody risks (centralized failure), while trustless bridges carry smart contract risks (code bugs). Users must evaluate the specific implementation and audit history of the specific tool they intend to use.
I guess we are supposed to feel excited about breaking our own infrastructure again
The irony of building complex solutions for simple problems is just getting old
We need to focus on basics before trying to connect everything to the moon
Security research feels like chasing ghosts while thieves walk through the front door
Hopefully someone learns something this time around
Sarcasm aside it is still an important topic for investors
You are missing the bigger picture entirely here folks
I built three bridges last year and none got hacked because I used the right architecture
Amateurs worry about bugs while professionals manage risk effectively
The market always filters out the weak players eventually
Don't let fear drive your investment strategy forward
Just stick with the audited protocols and you will be fine
Most people just want easy profits and then complain when reality hits hard
This industry rewards skill and punishes greed consistently
Keep that in mind before you panic sell everything today
I know the tech and that is why I win big
they dont want you moving money freely anywhere
government tracking tools love these bridge blind spots so much
privacy dies here slowly while central banks watch closer
why trust code written by strangers who might sell your data
its all part of the larger surveillance grid anyway
It is truly fascinating how much complexity we face today
We often ignore the foundational layers of code
The speed of development seems outpaced by security audits
You see protocols launching every single week
Yet the basic communication standards remain vague
This lack of uniformity creates friction for everyone involved
Developers waste time rewriting integration scripts
Resources could be better spent on actual user tools
Regulatory pressure adds unnecessary stress to operations
Companies hesitate to deploy because of legal ambiguity
Users suffer from confusing interfaces and error messages
Trust becomes difficult when systems fail frequently
We need more collaboration between competing networks
Isolated silos do not serve the broader ecosystem well
Hopefully future updates address these critical gaps soon
I believe standardization will save us eventually from chaos
Your point regarding standardization is exceptionally well articulated, indeed
Collaboration remains the primary hurdle for industry-wide adoption, as noted
The technical barriers are significant, yet surmountable with effort
Legal frameworks will likely evolve alongside technological improvements
We must proceed cautiously, balancing innovation with compliance requirements
A unified approach would significantly reduce the risk profile for enterprises
I appreciate your comprehensive overview of the situation here
Thank you for sharing such a thoughtful perspective on the matter
STOP TRUSTING THESE BRIDGES UNTIL THEY FIX THE CODE!!!!!
Exactly!!😂 The average person is way too dumb to handle this tech safely
Rich whales survive because they have teams to audit the mess
Why bother helping the small fish when sharks eat them anyway?
It is nature showing itself clearly in the crypto jungle today
Survival of the fittest applies here more than anywhere else
THIS IS DISASTER WAITING TO HAPPEN EVERYWHERE
THEY WILL ALL GET HACKED SOON AND WE LOSE EVERYTHING
I DONT WANT TO HEAR ANY EXCUSES FOR WHY IT WORKS NOW
MY MONEY GONE BEFORE IF I MOVE IT WRONG TEH
PLEASE READ THIS AGAIN AND REALIZE DANGER LEVELS HIGH
I hear your concern deeply regarding the potential loss
Cultural differences affect how we perceive financial risk globally
Some regions trust tech more than others unfortunately
We must respect those fears even if they seem exaggerated to engineers
Different backgrounds shape our reaction to these digital threats
test small amounts first always
read contract addresses twice before signing
use hardware wallets for bridge transactions
avoid rushed transfers during peak congestion times
gas fees kill smaller moves sometimes
People forget that centralized bridges are just custodial scams in disguise
They claim decentralization but hold keys in a single vault behind
Hackers know this weakness and target the weakest link every day
Complex proofs fail because developers rush releases to meet deadlines
There is no real incentive to build secure long term systems here
The money is made during the pump not the maintenance phase
Regulators ignore these flaws until the market crashes completely
I expect another billion dollar loss event before next fiscal year
you hurt me reading that but i agree deep down
hope things get better for us all someday soon
safety matters more than profit any day of the week
heart goes out to victims of these bad exploits everywhere
The essence of connection is finding trust in a chaotic world
We seek pathways that honor both speed and safety equally
Technology reflects our inner struggle between control and freedom
Bridges become metaphors for how we relate to each other now
Perhaps the solution lies in slowing down to go faster overall